THE STATE OF RANSOMWARE IN HOME AUTOMATION 2023
- March 31, 2022
- by Ezlo Admin
How close is the threat and what we can do about it?

IoT devices get regularly hacked, this is no news today. Sometimes they’re compromised due to curiosity, and sometimes to demonstrate a lack of protection. In worst cases, this is done to get a ransom for device unlocking, the malicious software used for this devious act is called ransomware.
When we talk about enterprise IoT, it seems that these problems don’t relate to the common user. Organizations are expected to take care of their security, so this is their headache, not ours.
When last November the San Francisco bus and train system was attacked by ransomware, managers made all rides free and left the buses and trains running while they fixed the problem. Not a big problem, so it seems.
But what will happen, if ransomware attacks devices in our houses? This is not a matter of if, but when, as there have already been precedents:
1) On January 2017, the first Android TV was reported infected with ransomware
2) Two guys at the Def Con hacking conference were able to install ransomware into a smart thermostat and lock it.
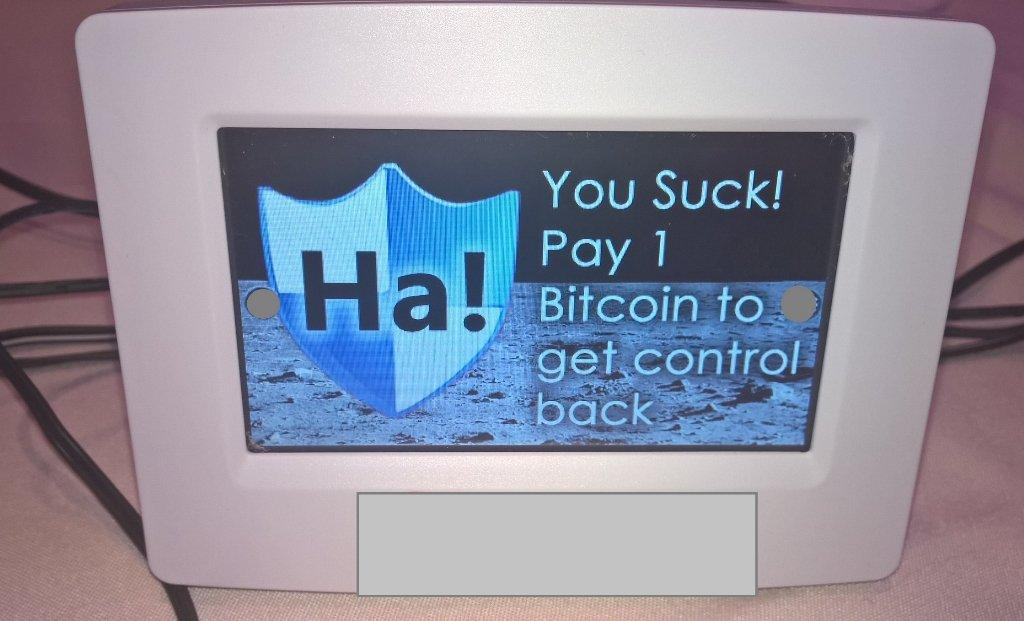
The ransomware message that Tierney and Munro were able to display on the vulnerable thermostat.
The TV owners were informed to make a factory reset, and you most probably can turn off the heating and call for a technician or a company engineer to fix your thermostat. But what if it’s your smart lock getting hacked and won’t let you in your apartment or out of it? What if your washing machine or fridge goes crazy and you get a message to pay the ransom, or otherwise your expensive piece of technology becomes useless?
Consider also that the hackers don’t even necessarily need to make a full-fledged incursion into your devices: sometimes it is enough to convince you that the situation is critical, that there’s an imminent threat.
Gib Scorebo, a chief cybersecurity strategist at Leidos, offered a hypothetical situation during a panel discussion at the RSA Conference in San Francisco on February 2017. Imagine an entertainment system in your car that suddenly prompts “Pay up or you are going to crash”. Will you be able to immediately cope with this sudden stress in the middle of driving and check if anybody has indeed taken control of your car?
With a smart home device, it might appear that you can always turn it off or make a factory reset (though ransomware may be potentially able to lock the device and not let you do this) or call a technician. But what if the ransom demand only asks for $50 or $25? If you’re in a hurry, you might find it easier to pay the ransom than google for a solution or call for help.
In her interview with SC Media ESET Security Researcher Lysa Myers told that this might be a very common scenario:
“Interrupting someone’s ability to control the comfort of their home, their ability to do the normal tasks of daily life like getting to work or doing laundry may not seem like a big deal but it could be just enough of an inconvenience to motivate people to pay.”
But it looks like this threat is not yet here. There are two reasons for that.
First, the most popular way to demand ransom and cover against money traces is to take advantage of cryptocurrencies. At the moment, the penetration of technology is too microscopic, people might not have crypto wallets yet and may not even know how to send crypto money.
Second, the examples above have flaws. The TV was running on Android, a system well-known for lots of viruses, trojans, and malware. No wonder the ransomware also sneaked into the list. And the smart thermostat worked on Linux and required physical access to get hacked. To make such a hack possible remotely, one would need to place ransomware in an image that the thermostat owner would want to download from the internet and upload onto the device via USB to use as wallpaper on its screen.
This doesn’t mean people can completely ignore the issue. But what they can do? Two options:
1) Factory reset, hidden recovery mode, etc. are techy things that are not so complicated to explain to a common user. Thus, manufacturers and installers can teach customers what to do if they noticed the suspicious activity of the device or were demanded to pay a ransom.
2) The devices themselves should be protected enough to avoid the possibility of ransomware hacks.
Since the device manufacturers are unable to promise top-notch security, there are solutions like Norton Core and F-Secure Sense, which are routers that filter the network traffic and focus on protecting smart home devices.
However, getting yet another utility device for a smart home network (in addition to a hub) makes the whole smart home concept even more complicated and doesn’t help popularize it.
In the end, it looks like the market is still awaiting for players who will be able to make a revolution in the security of smart home devices and guarantee protection from ransomware and other threats. Only then the users will finally widely adopt home automation technologies.
Related Resources:




